Set Up SSH Key Management
Foxpass helps users self-service their SSH key management and provides easy access services for servers. Additionally, Foxpass provides extra features like temporary access and pattern based host matching.
How to Configure Host Access Through Foxpass
- Integrate Foxpass with your hosts
- Run the Foxpass setup script on your current hosts. Then, see the 'Linux Configuration' section on the left-hand side for further instructions.
- Add the script into your startup script or a configuration management tool like Chef or Puppet. That way, whenever you spin up a new instance, it will already be configured with Foxpass.
- Generate & upload your SSH key
- Follow the instructions on 'Adding your SSH key to Foxpass' to generate and upload an SSH key from your computer to Foxpass. You can upload an existing public key if you have one already.
- Make sure your user type is set as 'Engineering' or else the SSH key management feature will not be available.
At this point, you should be able to log into any configured host using the SSH key you uploaded to Foxpass.
-
Next Steps: Extra options for more advanced users.
-
Set automatic SSH Key expiration. Go to the 'Config' page and go to the 'SSH Key expiration' panel to set an expiry. Users will automatically receive an email when their SSH key is about to expire with a prompt to upload a new one.
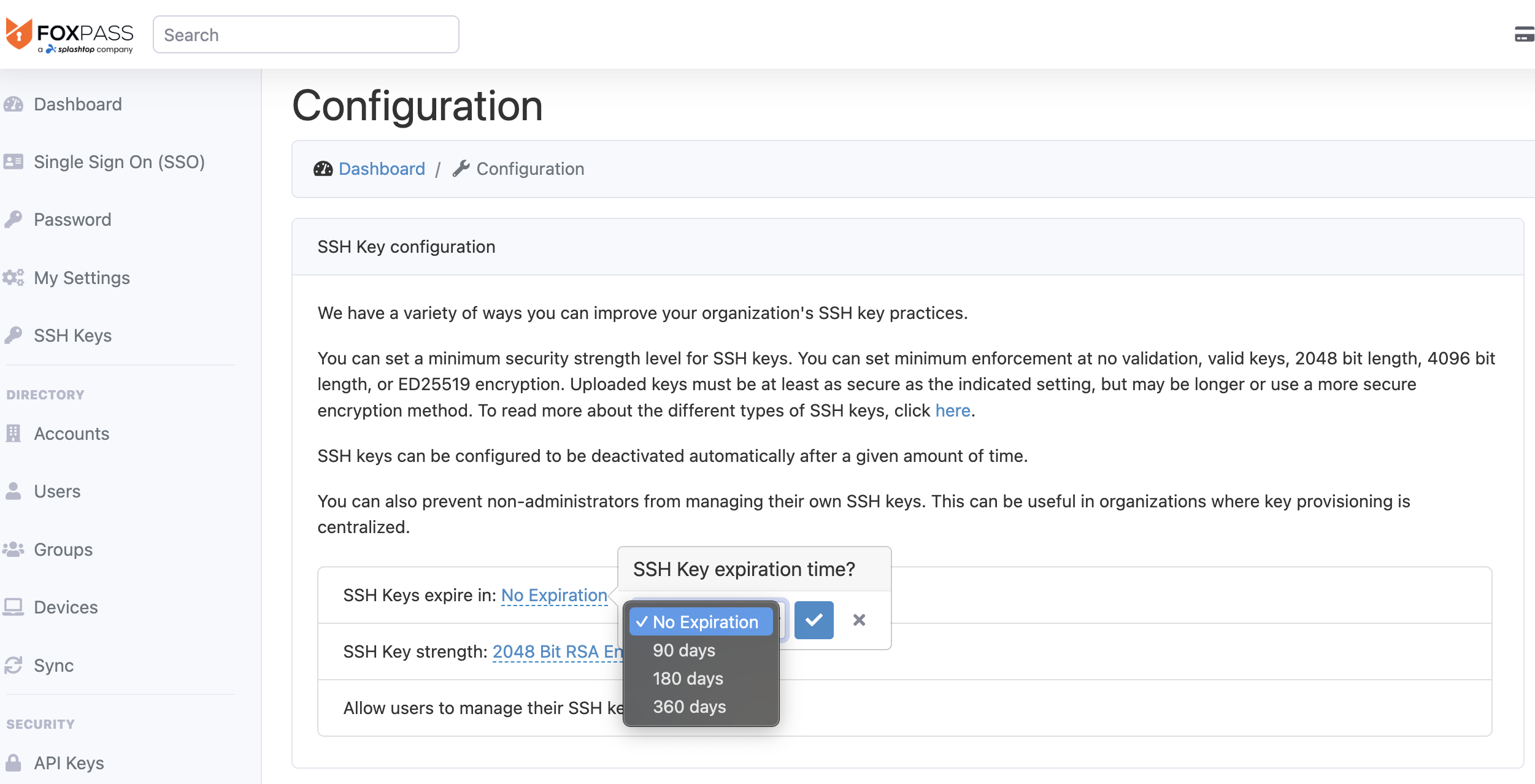
Set SSH Key expiration
-
Add a 'foxpass-sudo' group. If you'd like to run 'sudo' commands on the host without having to re-enter your password, create a group named 'foxpass-sudo' here. Add yourself or any other users who need easy Sudo access to the host as needed.
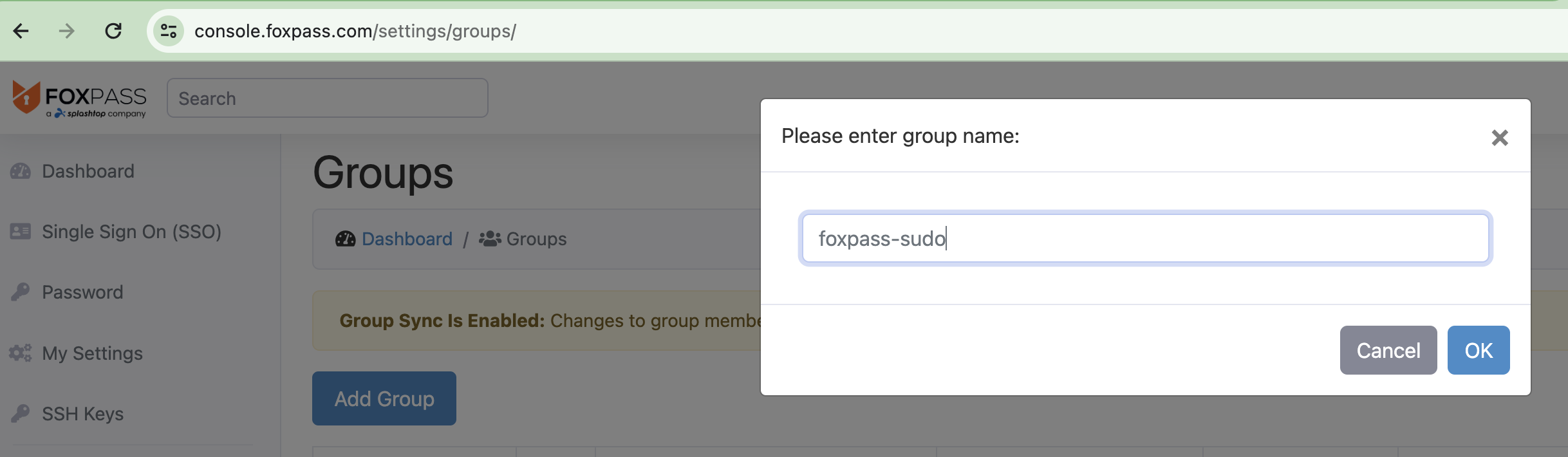
Add foxpass-sudo
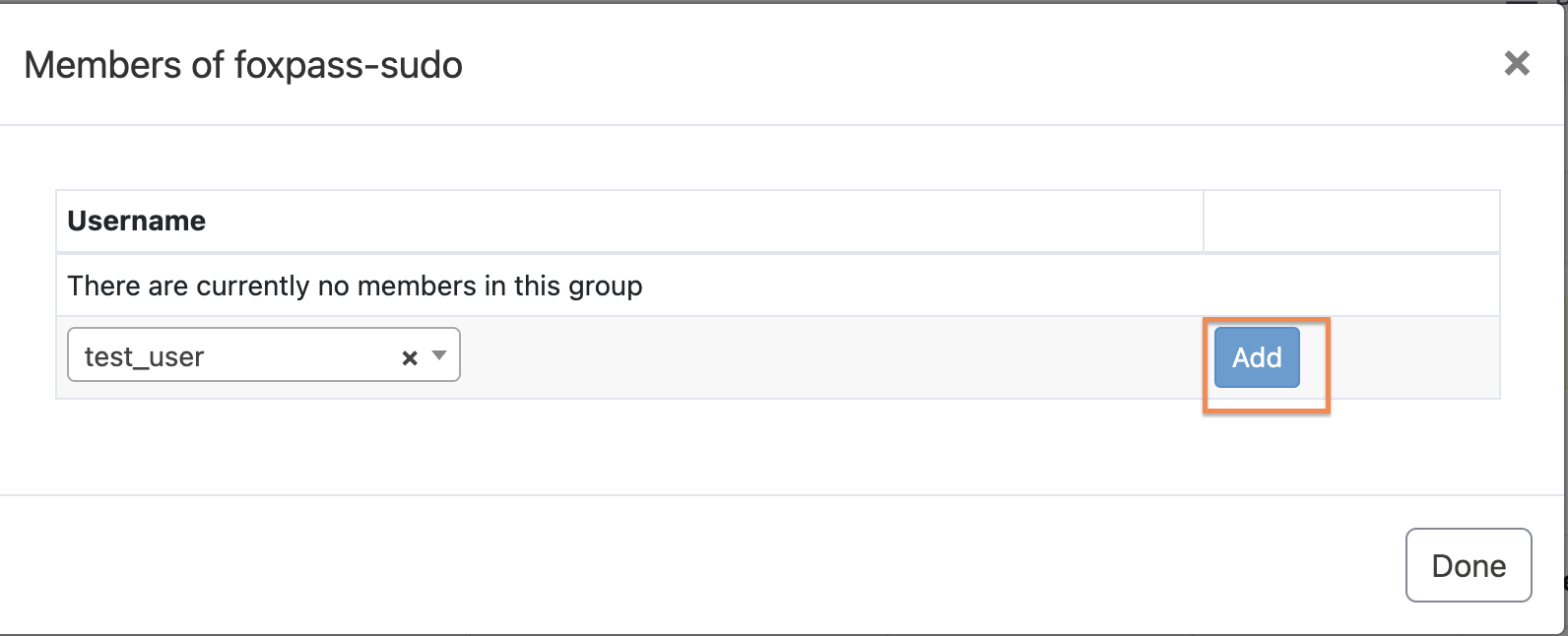
Add user to foxpass-sudo
-
Manage your organization. Admins can also manually manage other users' SSH keys from the 'Users' page under the 'Actions' dropdown. Admins can upload, enable, disable, or 1-click disable all SSH keys for a particular engineering user.
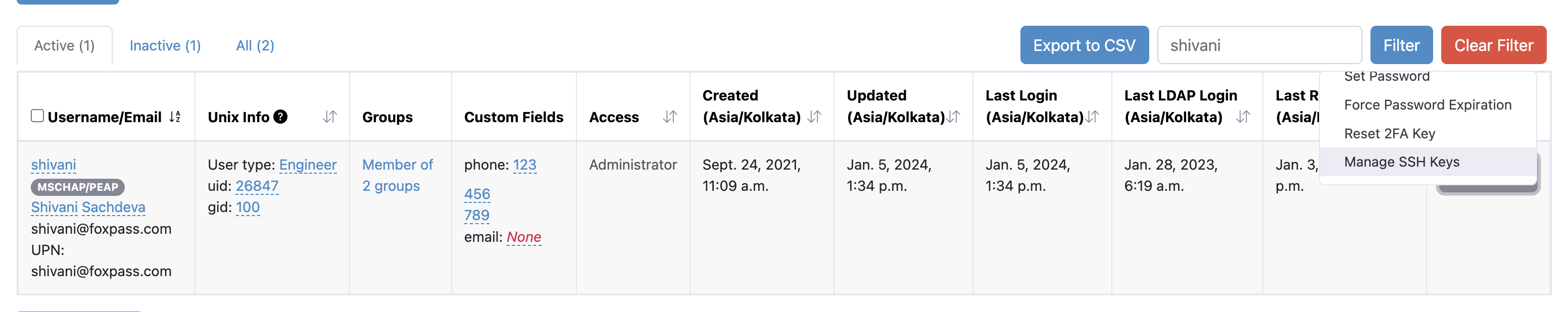
Click Manage SSH Keys
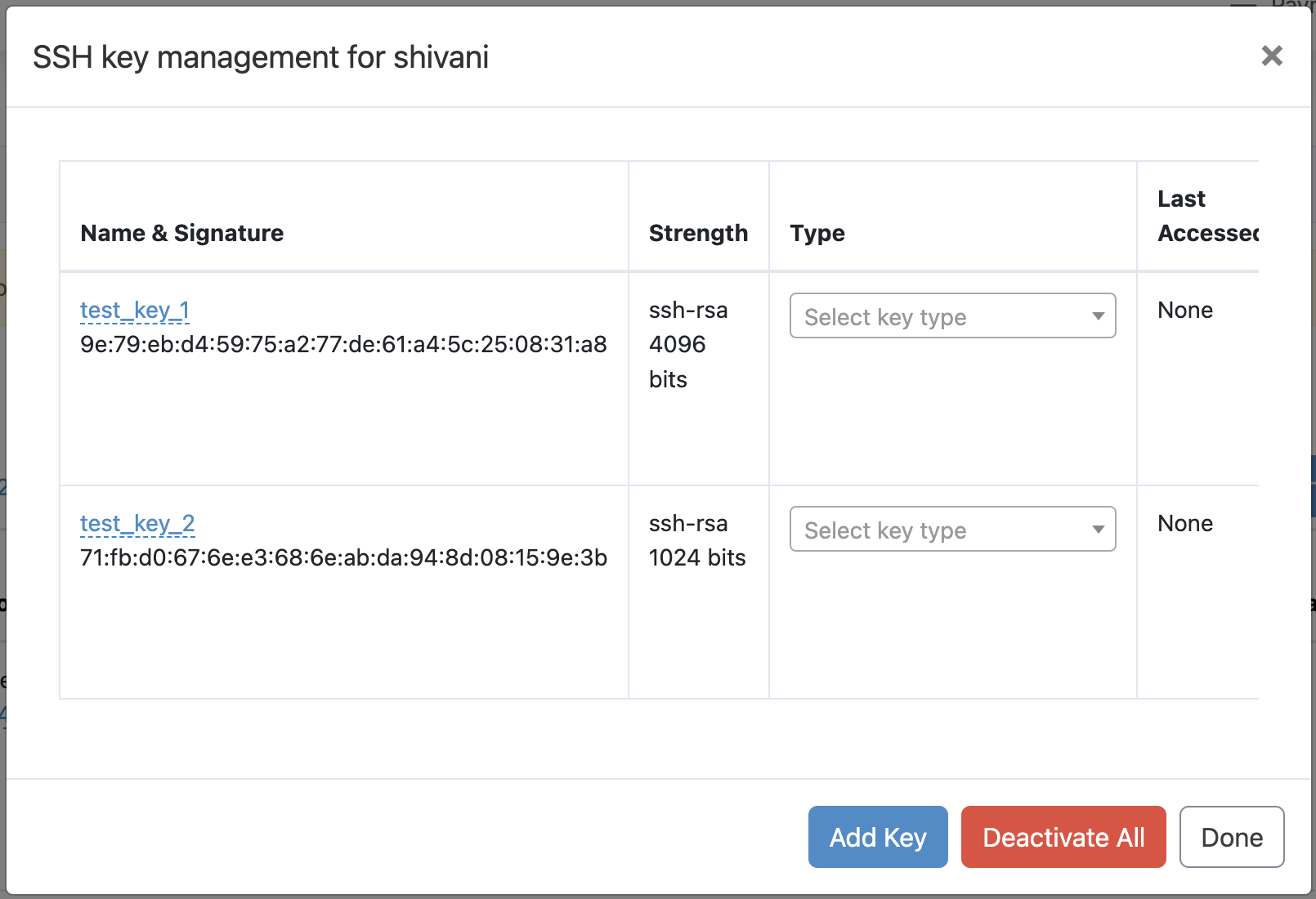
Manage SSH Keys
-
Enable host groups for temporary access controls. Host groups allow you to grant users or groups temporary or permanent access to your infrastructure. They're a great way to enforce the Principal of Least Privilege across your organization.
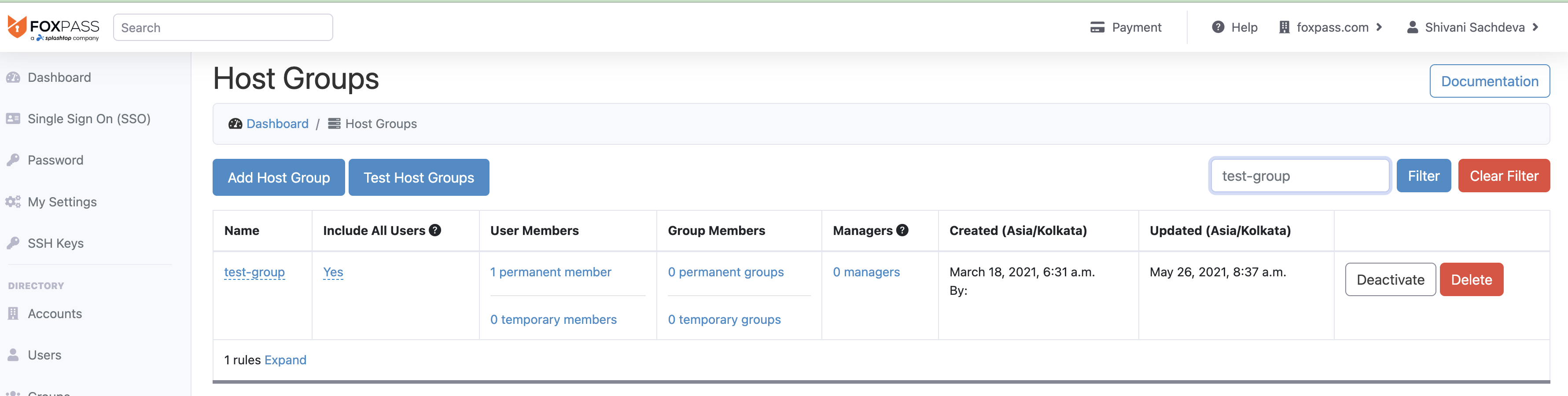
Sample hostgroup
-
Integrate with API to automate access. Check out the API endpoints for SSH keys here.
-
Updated about 2 months ago